ad-assurance - RE: [AD-Assurance] Radius NTLMv1
Subject: Meeting the InCommon Assurance profile criteria using Active Directory
List archive
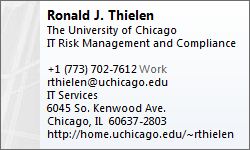
- From: Ron Thielen <>
- To: "" <>
- Subject: RE: [AD-Assurance] Radius NTLMv1
- Date: Fri, 31 Jan 2014 01:22:28 +0000
- Accept-language: en-US
|
Thanks for the comments David. We mention Radius in section 4.2.1, but the section where my comment becomes relevant is 5.2.3.
We recommend setting the LMCompatabilityLevel to 5 in 5.2.3.
One consequence of the point I’m raising is that if you do that and that domain is also used by Radius, then your Radius installation may well break.
Maybe it should be mentioned in Appendix A as a known issue.
(I was also looking for additional insight into the issue, or magic bullets.
It was raised as a point for discussion in the first AD Cookbook group, but we never actually got anywhere with it.
The discussion went something like “Q: Hey what about Radius?
A: Yep, there’s that.”) Regarding BitLocker:
At this point, I’m looking for opinions on the approach, so I appreciate your sharing yours.
I understand that there may be a lot of debate on this as an approach. If my physical access controls have been audited for FISMA moderate compliance, which they have, then I’d argue that should be good enough.
The alternative for me is to move a half dozen DCs to physical controllers and lose the benefits of virtualization, stand up a Hyper-V installation which we’re not planning, or gamble on some third party encryption product for VMWare like Porticor.
I think my approach represents the least risk for the institution, but we’re positioning ourselves for one of the alternatives if it’s rejected.
I don’t think we should mention media management controls until they are accepted as an alternative means.
Then we can update the doc if it seems appropriate. Ron
From:
[mailto:] On Behalf Of David Walker Ron,
I don’t think we ever sufficiently addressed the issue of Radius using NTLMv1 to talk with the DC. We address the fact that using PEAP-MS-CHAPv2 deals
with the communication between the supplicant and the Radius server, but Radius servers which rely on Samba use NTLMv1 between the Radius server and a DC. |
- [AD-Assurance] Radius NTLMv1, Ron Thielen, 01/29/2014
- [AD-Assurance] RE: Radius NTLMv1, Coleman, Erik C, 01/29/2014
- Re: [AD-Assurance] Radius NTLMv1, David Walker, 01/30/2014
- RE: [AD-Assurance] Radius NTLMv1, Ron Thielen, 01/30/2014
- Re: [AD-Assurance] Radius NTLMv1, David Walker, 01/31/2014
- Re: [AD-Assurance] Radius NTLMv1, Ann West, 01/31/2014
- Re: [AD-Assurance] Radius NTLMv1, David Walker, 01/31/2014
- RE: [AD-Assurance] Radius NTLMv1, Ron Thielen, 01/30/2014
Archive powered by MHonArc 2.6.16.